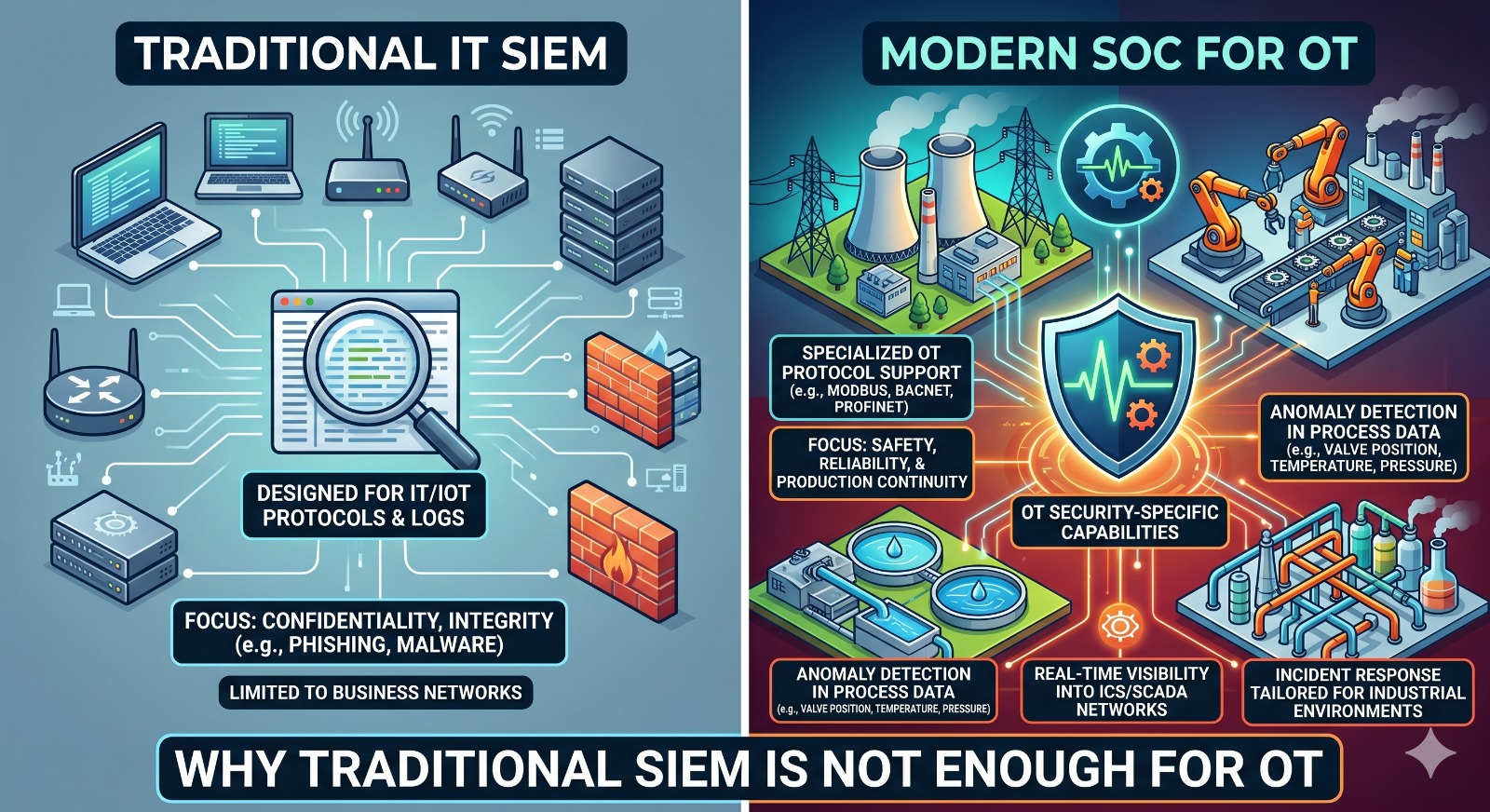
In today’s interconnected industrial landscape, operational technology (OT) systems are increasingly targeted by cyberattacks. While Security Information and Event Management (SIEM) systems have been the cornerstone of IT security for years, they are often insufficient for protecting critical infrastructure. This article explores why a traditional SIEM falls short when it comes to OT environments and why a specialized Security Operations Center (SOC) is necessary.
The Challenge of OT Environments
OT systems, such as industrial control systems (ICS) and supervisory control and data acquisition (SCADA) networks, manage and monitor physical processes in sectors like energy, manufacturing, and transportation. Unlike IT environments, where data confidentiality and availability are paramount, OT prioritized safety, reliability, and continuous operation. Attacks on OT can have devastating physical consequences, leading to equipment damage, production downtime, and even danger to human life.
Traditional SIEM: Built for IT, Not OT
Traditional SIEMs are designed to collect and analyze logs and events from IT systems, such as servers, endpoints, and applications. They rely on standardized protocols and data formats to identify security incidents. However, OT networks are vastly different from IT networks, making it difficult for traditional SIEMs to provide effective monitoring:
-
Proprietary Protocols: OT devices often use proprietary communication protocols that are not recognized by IT SIEMs. This makes it challenging to collect and interpret relevant security data.
-
Lack of Visibility: Traditional SIEMs often lack deep visibility into OT networks, making it difficult to detect sophisticated attacks that target specific OT devices or processes.
-
Contextual Misunderstanding: IT SIEMs are not equipped to understand the operational context of OT systems. They may misinterpret normal process fluctuations as security alerts, leading to false positives and alert fatigue.
-
Inability to Analyze Process Data: OT security requires analysis of process data, such as sensor readings and actuator states, to detect anomalies. Traditional SIEMs are not designed for this type of analysis.
The Role of a Specialized OT SOC
A specialized OT SOC is crucial for providing the visibility, expertise, and response capabilities needed to protect critical infrastructure. Key features of an effective OT SOC include:
-
OT-Specific Tools and Technologies: Utilizing OT-native security tools, such as industrial intrusion detection systems (IDS) and asset discovery solutions, that are designed for industrial environments.
-
Deep OT Visibility: Gaining comprehensive visibility into OT networks, including asset inventory, protocol analysis, and process monitoring.
-
OT-Specific Threat Intelligence: Leveraging threat intelligence tailored to industrial environments to identify relevant threats and attack vectors.
-
Skilled OT Security Professionals: Having a team of security analysts with expertise in OT systems, industrial protocols, and ICS/SCADA security.
-
Integration with IT Security: Establishing clear communication channels and integrated workflows between IT and OT security teams to ensure a unified defense strategy.
By implementing a specialized SOC for OT, organizations can proactively detect and respond to cyber threats, mitigating the risk of operational disruptions and ensuring the safety and reliability of their critical infrastructure.
