In the realm of modern manufacturing, energy, and utility sectors, the invisible backbone is composed of Programmable Logic Controllers (PLCs) and Distributed Control Systems (DCSs). These specialized computing systems bridge the digital and physical worlds, automating complex processes.
However, as these traditionally isolated systems become increasingly connected to corporate networks and the internet, they are exposed to a new frontier of cybersecurity threats. Understanding their common vulnerabilities is the first step toward building a resilient industrial infrastructure.
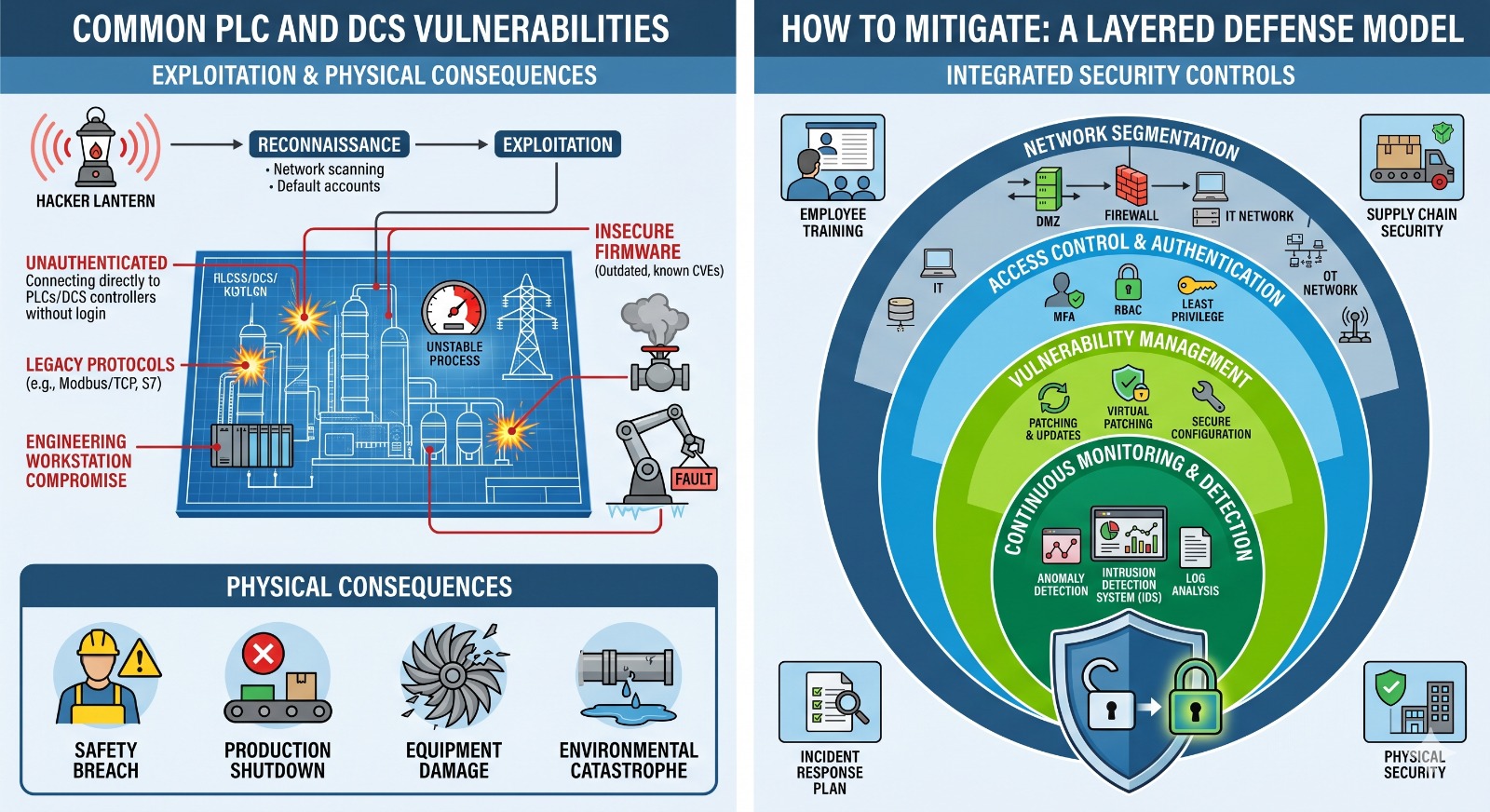
The Illustrated Landscape of Industrial Cyber Risk
This infographic visualizes the ecosystem of PLC and DCS security. It highlights the main stages of an attack: reconnaissance, exploitation of known weaknesses, and the severe physical consequences. It also illustrates the foundational pillars of mitigation.
Visualizing the Problem and Solution
The top panel, Attack Surface and Consequences, maps the journey of a threat from external networks into the heart of a control system, showing how digital tampering can lead to tangible results like physical damage, safety breaches, or complete process shutdown.
The bottom panel, Integrated Mitigation Strategy, presents a layered defense model. It emphasizes that no single solution is enough. A robust posture requires an integrated approach that spans network architecture, access control, continuous monitoring, and structured maintenance.
Common PLC and DCS Vulnerabilities
PLC and DCS vulnerabilities are unique because they exploit the nature of real-time control. A vulnerability on a desktop computer might leak a password; a vulnerability on a controller can stop a plant.
| Vulnerability Type | Description & Impact |
| Insecure/Legacy Protocols | Industrial communication protocols like Modbus/TCP, EtherNet/IP, and PROFINET were designed for speed and reliability, often without authentication or encryption. This allows attackers to easily intercept traffic, inject fake data, or replay commands to manipulate the process (e.g., False Data Injection Attack). |
| Unauthenticated Access & Default Accounts | Many controllers and engineering workstations ship with default vendor credentials that are never changed. Even worse, some critical function paths have insufficient authentication enforcement, allowing an attacker to bypass requirements entirely. This provides an open door to modify logic or configurations. |
| Outdated Firmware & Unpatched Systems | Like all computers, PLCs have software (firmware) that requires updates. Organizations often delay patching due to concerns about operational downtime or incompatibility. This leaves known CVEs unaddressed, which attackers can exploit (e.g., memory corruption leading to out-of-bounds writes or Denial-of-Service). |
| Compromised Engineering Workstations | These high-value targets are the only devices authorized to program and manage the controllers. If an attacker gains access to a workstation, they can modify the entire industrial process, disable safety functions, and even weaponize the PLC against other parts of the network (e.g., ‘Evil PLC Attack’). |
| Weak Network Segmentation | When the IT (Corporate) and OT (Operational) networks are not properly isolated, a malware infection or ransomware on an employee’s laptop can spread laterally to the control network, halting critical operations or safety systems. |
How to Mitigate: A Layered Defense Model
Mitigating these risks requires moving away from the “air gap” mentality, which is no longer effective in a connected world. A more resilient model uses a ‘Defense-in-Depth’ approach, layering multiple, independent security controls.
1. Robust Network Segmentation
The most effective initial step is to logically and physically isolate the Operational Technology (OT) network from the IT network. Use industrial firewalls to create distinct security zones (e.g., following the ISA/IEC 62443 standard), allowing only essential traffic to pass. Establish a Demilitarized Zone (DMZ) to facilitate secure data transfer between the zones without direct connectivity.
2. Access Control and Strong Authentication
Implement strict access controls based on the Principle of Least Privilege. Grant users and devices only the minimal permissions required for their specific role. Enforce Multi-Factor Authentication (MFA) for all remote access and for accessing critical systems like engineering workstations, particularly when connecting across network zones. All default passwords must be changed.
3. Vulnerability and Patch Management
Establish a proactive process for tracking and remediating known weaknesses. Maintain a comprehensive, dynamic asset inventory of all hardware, software, and firmware. Regularly review vendor security advisories. When traditional patching of a critical device is not feasible due to downtime constraints, deploy Virtual Patching using an inline Intrusion Prevention System (IPS) to block exploitable traffic before it reaches the vulnerable target.
4. Continuous Monitoring and Anomaly Detection
To catch an attack, you must be able to see it. Deploy specialized industrial monitoring tools and an Intrusion Detection System (IDS) to monitor network traffic for abnormal behaviors. Unlike traditional IT security, OT anomaly detection can identify non-compliant communication protocols, unauthorized device connections, unusual increases in command frequency, or attempts to modify control logic, alerting operators to a potential threat in real-time.
