As we move deeper into 2026, the landscape of Industrial Control Systems (ICS) and Supervisory Control and Data Acquisition (SCADA) systems face a new and unprecedented level of risk. The air gaps and security-by-obscurity that once protected critical infrastructure have largely vanished, replaced by a hyper-connected, data-driven industrial ecosystem. While the digital transformation delivers efficiency, it simultaneously creates a broader attack surface for increasingly sophisticated adversaries.
The threats targeting these essential systems have evolved, leveraging cutting-edge technologies and new operational realities. To stay resilient, security professionals must understand these emerging vectors. Here are the top 10 cyber threats targeting ICS and SCADA systems in 2026.
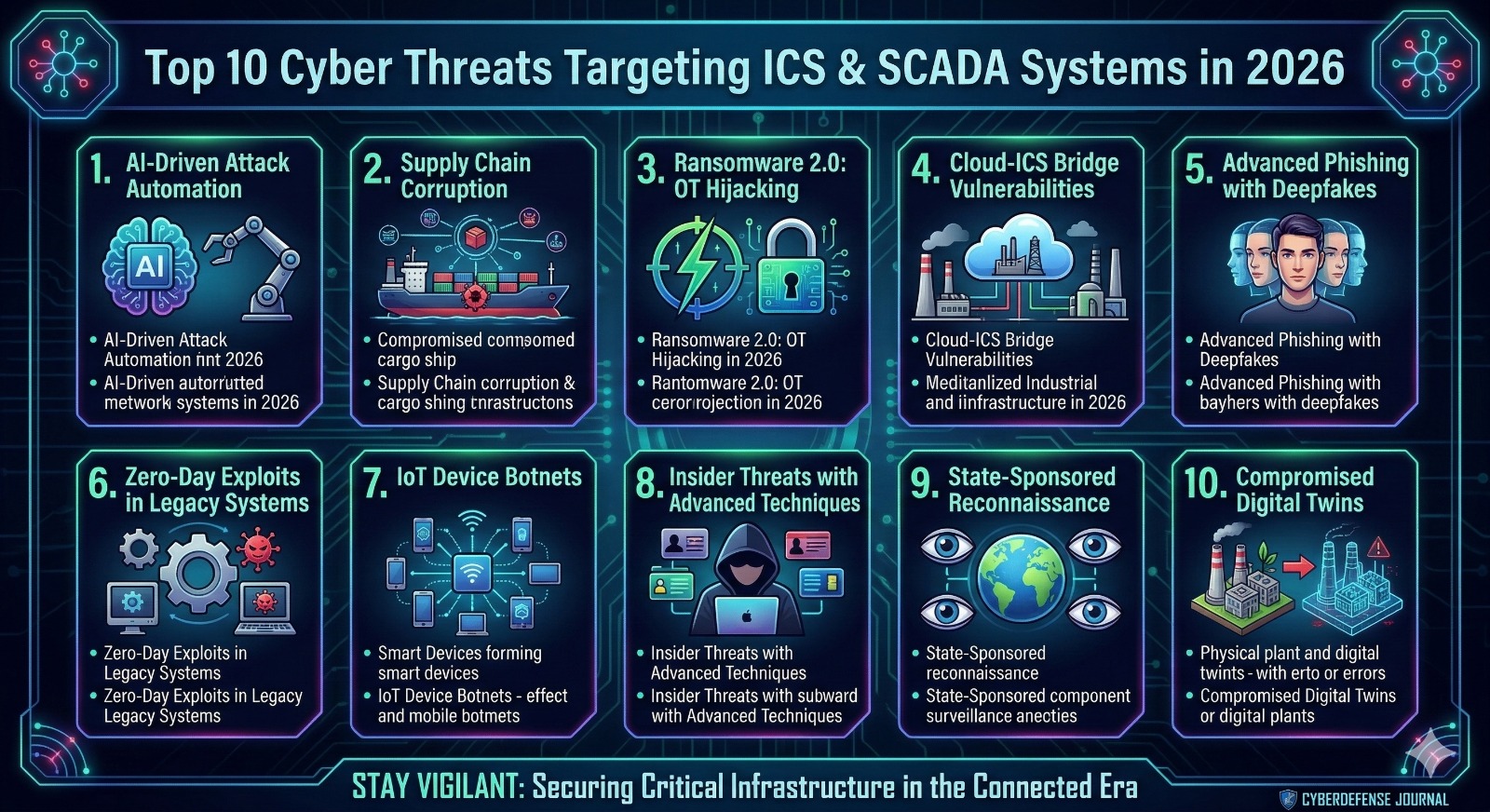
1. AI-Driven Attack Automation
Artificial Intelligence (AI) has become a double-edged sword. Threat actors are now using AI-powered tools to automate the entire attack lifecycle, from reconnaissance to execution. These intelligent algorithms can scan entire networks, identify vulnerabilities, and craft unique exploits in minutes, a process that used to take days or weeks. Furthermore, AI can be used to adapt and morph malware in real-time, making it nearly impossible for static, signature-based defenses to detect and stop attacks. The speed and adaptability of AI-driven attacks represent a quantum leap in the threat against industrial networks.
2. Supply Chain Corruption
The industrial supply chain, a complex web of vendors, manufacturers, and service providers, has become a primary attack vector. In 2026, attackers are increasingly corrupting the hardware and software components before they even reach the facility. Compromised microprocessors, tampered firmware, and backdoored ICS software can lie dormant, evading all standard inspections until they are triggered. The increasing reliance on global, just-in-time logistics makes it incredibly challenging to verify the integrity of every single component in a critical system.
3. Ransomware 2.0: OT Hijacking
Ransomware has evolved from simple data encryption to direct, operational hijacking. In 2026, threat actors aren’t just locking up files; they are directly seizing control of programmable logic controllers (PLCs), human-machine interfaces (HMIs), and other core Operational Technology (OT) assets. They demand a ransom not just to decrypt data, but to restore a chemical process, a power grid, or a manufacturing line. This direct, operational blackmail puts immense pressure on organizations, as downtime can lead to billions in lost revenue, physical safety risks, and environmental catastrophes.
4. Cloud-ICS Bridge Vulnerabilities
The adoption of hybrid cloud models, where some ICS functions and data are moved to the cloud, has introduced new and serious risks. While the cloud offers scalability and advanced analytics, it also creates a complex bridge that is often poorly secured. Weak application programming interfaces (APIs), misconfigured access controls, and vulnerabilities in cloud management platforms are being exploited. Compromising the cloud component can provide an easy back door into the core industrial control network, bypassing traditional perimeter defenses.
5. Advanced Phishing with Deepfakes
Phishing has become a sophisticated craft, utilizing highly realistic deepfake technology. Attackers are using AI to create convincing video and audio impersonations of high-level executives, trusted engineers, or key vendors. These deepfakes are used to build trust, trick personnel into sharing credentials, or tricking operators into clicking malicious links. The human element, already a significant vulnerability, has been further exploited by the inability to easily distinguish real communication from AI-generated deception.
6. Zero-Day Exploits in Legacy Systems
A perennial problem, the issue of legacy systems is more acute in 2026. Decades-old equipment, running proprietary or obsolete operating systems, remains the backbone of many critical facilities. These systems are rarely, if ever, patched. Attackers are specifically targeting these systems with new, previously unknown zero-day exploits. The difficulty of modernizing this equipment, combined with the lack of available support, means that these vulnerabilities are incredibly hard to defend against.
7. IoT Device Botnets
The proliferation of Internet of Things (IoT) devices on industrial sites has been a massive security blind spot. Industrial facilities are now filled with connected sensors, cameras, and building management systems that are often poorly secured. Attackers are harvesting these weak devices to build massive botnets. These botnets are used to launch overwhelming Distributed Denial of Service (DDoS) attacks against a facility’s own network infrastructure, or as a command-and-control platform to move laterally into the more sensitive OT networks.
8. Insider Threats with Advanced Techniques
The risk from within remains one of the most dangerous. In 2026, insider threats have become more sophisticated. Disgruntled employees or contractors can now use readily available AI tools and scripting languages to automate their malicious actions, making them harder to detect. Moreover, attackers are using social engineering and blackmail to coerce legitimate insiders into granting access or installing malware. Modern insider threats are less about brute-force sabotage and more about subtle, precise manipulation of control parameters over an extended period.
9. State-Sponsored Reconnaissance
Nation-states are engaged in persistent, long-term reconnaissance and pre-positioning on critical infrastructure networks. These groups invest heavily in staying silent, building a deep understanding of specific industrial processes and safety systems. Their goal isn’t immediate sabotage, but rather to establish a foothold and a complete “battlefield preparation.” By mapping every piece of equipment and understanding its operation, they hold the power to cause maximum disruption at a time of their choosing, during a geopolitical conflict.
10. Compromised Digital Twins
The use of digital twins—detailed, real-time virtual models of physical systems—is now a standard industry practice. However, this has created a new, high-value target. Attackers can now target and compromise the digital twin. By altering the virtual model, they can feed incorrect data back to the physical system operators, mask malicious changes in the real plant, or even create a feedback loop that leads to physical failure. A compromised digital twin means that what the operator sees on their screen no longer reflects reality.
Stay Vigilant: Securing Critical Infrastructure
The threats in 2026 are complex, interconnected, and highly automated. Defending against them requires a holistic and persistent security strategy. The traditional approach of isolating OT networks is no longer sufficient. Organizations must embrace a new model that focuses on visibility, proactive threat intelligence, and a security culture that extends from the boardroom to the control room floor.
Securing critical infrastructure in the connected era is not just a technological challenge; it is a vital prerequisite for national security and economic prosperity. Staying vigilant is not just an option—it is a necessity.
