Providing remote access to third-party vendors is essential for modern Operational Technology (OT) environments, enabling efficient maintenance, troubleshooting, and support for critical systems. However, balancing operational needs with robust security is a significant challenge. Unsecured remote access pathways can become primary attack vectors, potentially leading to costly downtime, safety incidents, or data breaches.
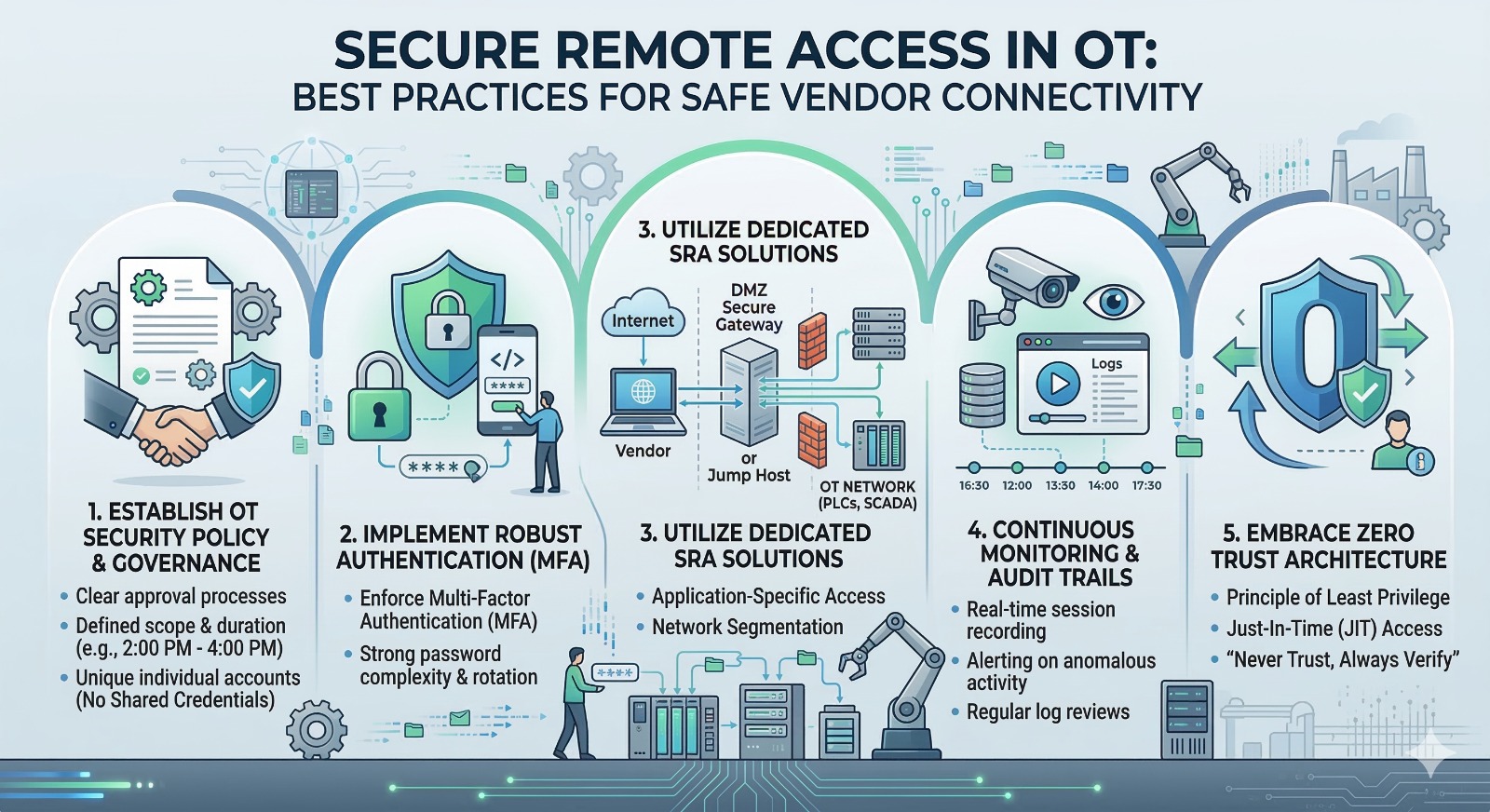
To mitigate these risks, organizations must implement a comprehensive strategy for safe vendor connectivity. Here are key best practices for securing remote access in OT:
1. Establish a Strong OT Security Policy & Governance
Before deploying any technical solutions, establish clear policies and procedures governing remote access. This should include:
-
Approval Processes: Require explicit approval and documentation for all vendor remote access requests.
-
Defined Scope & Duration: Clearly define the specific systems vendors can access, the tasks they are authorized to perform, and the precise timeframe for their access (e.g., specific dates and times). Avoid permanent, always-on connections.
-
Individual Accounts (No Shared Credentials): Mandate unique, individual accounts for every vendor employee accessing the OT network. Never use shared credentials (like ‘admin’ or ‘vendor’), as this makes auditing and attribution impossible.
2. Implement Robust Authentication (Multi-Factor Authentication)
The foundation of secure access is robust authentication. Relying on usernames and passwords alone is insufficient for OT environments.
-
Enforce MFA: Require Multi-Factor Authentication (MFA) for all remote access connections. This adds an essential layer of security, requiring vendors to provide two or more forms of verification (e.g., a password plus a one-time code from a mobile app or a physical token).
-
Strong Password Policies: Implement strict password complexity requirements and rotation policies for vendor accounts.
3. Utilize Dedicated Secure Remote Access (SRA) Solutions
Avoid using generic remote desktop protocol (RDP) or Virtual Private Networks (VPNs) configured to connect directly to sensitive OT assets. Specialized OT SRA solutions provide crucial security layers:
-
Gateway-Based Access: Use a dedicated secure gateway or jump host positioned within a DMZ (Demilitarized Zone) to broker connections. Vendors connect to the gateway first, which then facilitates the secure connection to the target asset, isolating the internal OT network from the internet.
-
Application-Specific Access: Limit vendor access to only the specific applications or protocols required for their work (e.g., granting access to a specific PLC programming software rather than full network visibility).
-
Network Segmentation: Ensure the OT network is properly segmented, and remote access pathways are restricted to authorized segments only.
4. Continuous Monitoring & Detailed Audit Trails
Visibility is crucial for security and accountability. Implement continuous monitoring and comprehensive logging for all vendor remote access sessions:
-
Session Recording: Record all remote access sessions in real-time (e.g., video capture of screen activity, keystroke logging) to provide a forensic audit trail of all vendor actions.
-
Real-Time Alerts: Configure alerts for anomalous activity, such as access attempts outside of scheduled times, unauthorized file transfers, or connections to unauthorized assets.
-
Regular Log Reviews: Regularly review access logs and session recordings to ensure compliance with security policies and identify potential issues.
5. Embrace a Zero Trust Architecture
Adopt a Zero Trust approach for remote vendor access. This means shifting from a perimeter-based security model to one that emphasizes “never trust, always verify.”
-
Least Privilege Access: Grant vendors the minimum level of access required to perform their specific tasks. If a vendor only needs to monitor data from a PLC, they should not have administrative privileges on the SCADA server.
-
Just-In-Time (JIT) Access: Implement JIT access, which provides access for a limited time only when needed, and automatically revokes it once the task is complete.
By following these best practices, OT organizations can successfully balance operational efficiency with the critical need to protect their infrastructure from cyber threats associated with vendor connectivity.
