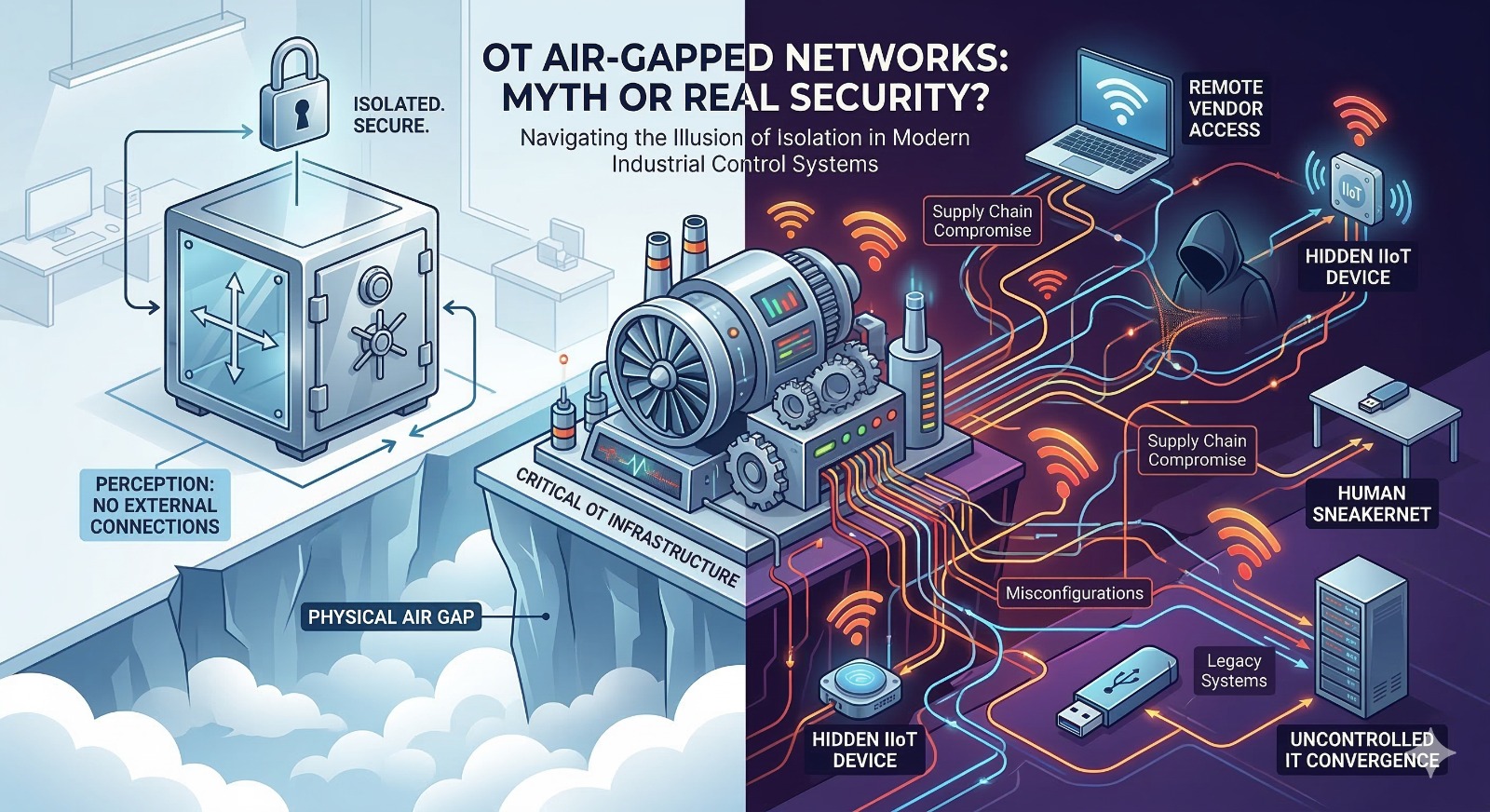
The concept of an “air-gapped” network – physically isolating a network from external connections, including the internet and less secure internal networks like corporate IT – has long been a cornerstone of industrial cybersecurity strategy. In Operational Technology (OT) environments, managing critical infrastructure like power grids, manufacturing plants, and transportation systems, the idea of absolute isolation seems like the ultimate defense against cyberattacks.
However, as OT systems become increasingly integrated with Information Technology (IT) and the broader internet, the effectiveness and even the feasibility of true air-gapping are being questioned. Is the air-gapped network in OT a crucial security measure or an outdated myth? The reality lies somewhere in between, requiring a nuanced understanding of modern industrial networks.
The Original Appeal of the Air Gap
Historically, OT systems were designed with proprietary protocols and hardware, operating in silos often without any external connectivity. Securing these systems primarily involved physical access control – locking doors and guarding facilities. As networking capabilities were introduced, physical isolation (the air gap) became the primary cybersecurity control. The logic was simple: if a network has no path from the outside world, no external attacker can reach it.
For decades, this approach provided a strong level of security. It was a tangible, easily understood concept that aligned well with the physical security mindset of industrial operations.
The Myth of Absolute Isolation
The modern reality, however, challenges the concept of a perfectly air-gapped network. The increasing demand for efficiency, data-driven decision-making, and remote access has driven a significant convergence between IT and OT systems. Several factors contribute to why true air gaps are often a myth today:
1. IT/OT Convergence and Business Needs
To optimize operations, industrial companies require real-time data from the factory floor to be analyzed by corporate applications. Production metrics, inventory levels, and predictive maintenance data need to flow from OT to IT systems, creating logical – and sometimes physical – connections. Business requirements often outweigh the desire for absolute network isolation.
2. The Rise of IIoT and Connectivity
The Industrial Internet of Things (IIoT) involves deploying sensors and devices with embedded connectivity (Wi-Fi, cellular, etc.) directly into OT environments. These devices frequently communicate with cloud platforms for data storage, analysis, and management, bypassing traditional network perimeters and potentially introducing new vectors for attack.
3. Remote Access for Maintenance and Support
Modern industrial equipment often requires specialized vendor support for maintenance, troubleshooting, and software updates. In the past, this might have involved technicians traveling on-site. Today, remote access solutions are standard, providing vendors with pathways into critical OT networks that, if improperly secured, can be exploited.
4. The Human Factor and “Sneakernet”
Even a seemingly air-gapped network is vulnerable to human error and deliberate circumvention. Employees and contractors may use removable media (USB drives, laptops) to transfer files, install software updates, or extract data. These “sneakernet” bridges are notorious vectors for malware. A compromised device plugged into an isolated network can have devastating consequences.
5. Supply Chain Compromise
The integrity of an air-gapped network is also dependent on the security of its supply chain. Malware can be pre-installed on hardware or software during the manufacturing or distribution process, lying dormant until the asset is deployed within the “secure” OT environment.
The Role of Air Gaps in a Defense-in-Depth Strategy
Despite these challenges, calling the air gap a complete myth is an oversimplification. Physical and strong logical segmentation are still crucial components of a robust cybersecurity strategy. While absolute isolation may be unachievable or impractical for most modern OT networks, the principles of the air gap retain significant value:
1. Reducing Attack Surface
A well-implemented segmentation strategy drastically reduces the available attack surface. While a few sanctioned connections may exist, they are tightly controlled, monitored, and restricted compared to a fully flattened network architecture.
2. Containing Breaches (Lateral Movement)
One of the most significant benefits of strong segmentation is containment. If an attacker manages to compromise a device in one segment (e.g., a corporate workstation or an IIoT device), effective segmentation prevents them from easily moving laterally into critical control networks.
3. Enforcing Strict Access Controls
Where connections are necessary (e.g., for data transfer from OT to IT), technologies like data diodes, unidirectional gateways, and hardened industrial firewalls can strictly enforce security policies, allowing data flow only in one direction and preventing command-and-control communication back from an external network.
Moving Beyond the Simple Air Gap
Recognizing that perfect isolation is often untenable, industrial organizations must adopt a more pragmatic, risk-based approach to OT security that incorporates segmentation within a broader defense-in-depth framework:
-
Risk Assessment: Conduct thorough risk assessments to understand critical assets, potential attack vectors, and the business impact of security incidents.
-
Strong Logical Segmentation: Instead of aiming for perfect physical air gaps, implement rigorous logical segmentation using virtual LANs (VLANs), firewalls, and access control lists (ACLs) to partition networks based on function and criticality.
-
Zero Trust Architecture: Apply Zero Trust principles, treating all devices and users (both internal and external) as untrusted until verified and authorized.
-
Continuous Monitoring and Visibility: Deploy network monitoring and anomaly detection solutions designed specifically for OT protocols to gain visibility into network activity and identify threats in real time.
-
Secure Remote Access: Implement secure, monitored, and audited remote access solutions (like jump servers with multi-factor authentication) that limit vendor access only to necessary systems and for limited durations.
-
Strict Control Over Removable Media: Establish and enforce policies and technical controls to manage the use of USB drives and other removable media, including scanning for malware before they are allowed near OT systems.
-
Supply Chain Security Management: Implement processes to verify the security integrity of software, firmware, and hardware acquired from suppliers.
-
Incident Response Planning: Develop and regularly test incident response plans tailored to OT environments, ensuring personnel understand how to react to and recover from cyber incidents impacting physical processes.
Conclusion
The concept of a perfectly air-gapped network in modern OT environments is largely a myth. The operational realities of connectivity and integration make absolute isolation impractical and often impossible. However, dismissing the air gap entirely is also dangerous.
Strong network segmentation and physical isolation where practical are still vital security controls. The value of the air gap today lies not in achieving absolute isolation, but in its ability to significantly reduce risk, contain breaches, and enforce granular security policies within a comprehensive, defense-in-depth approach tailored to the unique challenges of operational technology.
