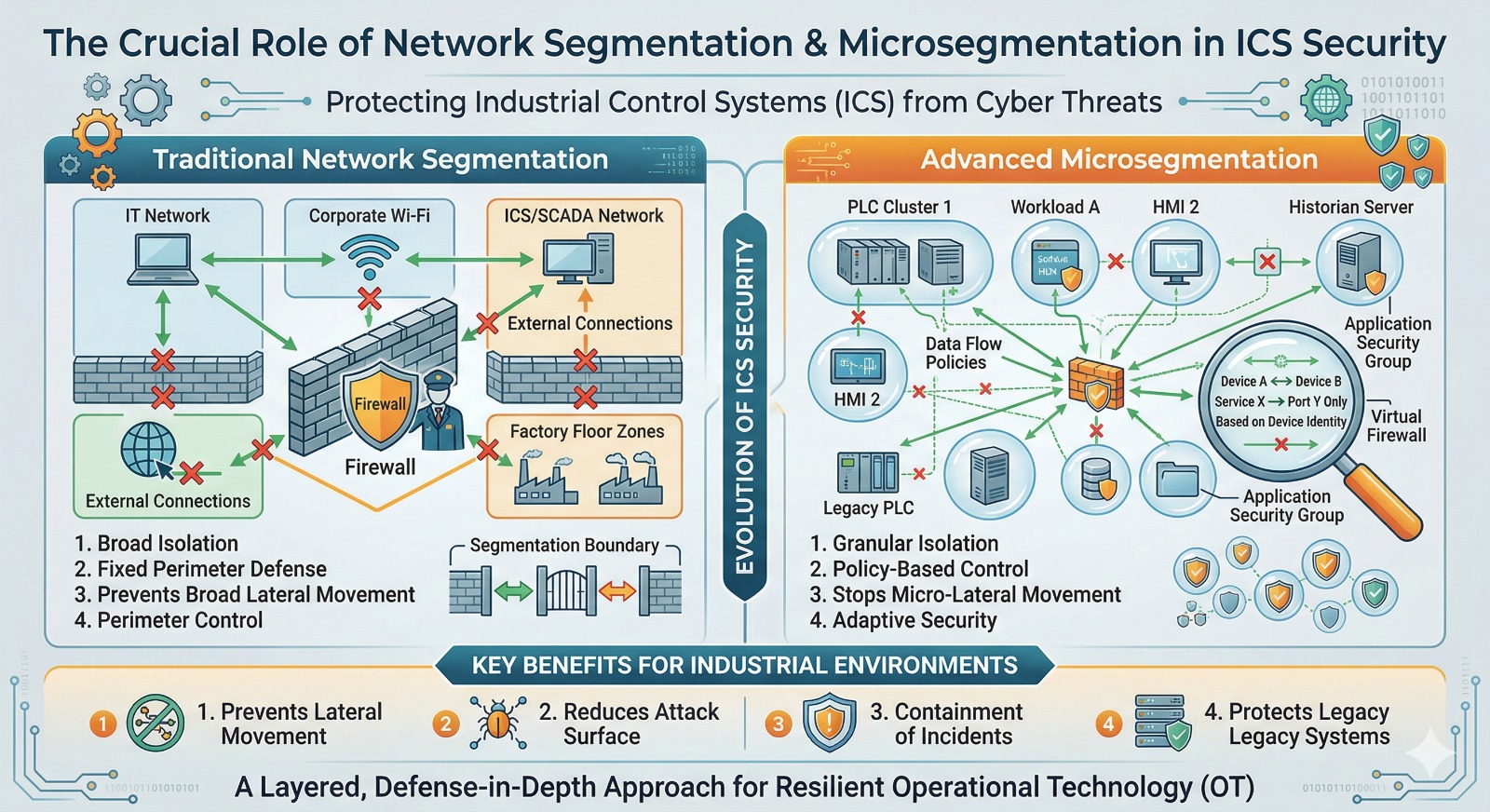
Industrial Control Systems (ICS) are the lifeblood of modern critical infrastructure, managing everything from power grids and water treatment plants to manufacturing lines and transportation networks. Historically, these systems relied on “security through obscurity,” operating in isolated environments. However, the relentless march of digitalization and the “Industrial Internet of Things” (IIoT) have interconnected ICS with corporate networks and the internet, opening a Pandora’s box of cyber vulnerabilities. A breach in an ICS can have catastrophic, real-world consequences, far beyond mere data loss. This is where network segmentation and its more granular evolution, microsegmentation, become indispensable pillars of an effective ICS security strategy.
Understanding the Landscape: The OT/IT Convergence and Air Gaps
Traditional ICS, often referred to as Operational Technology (OT), were designed with performance, reliability, and safety as the primary goals. Security was an afterthought, based on the assumption that the systems were physically and logically separated from IT networks – the famous “air gap.”
However, the air gap is a myth in most modern industrial settings. The need for real-time data analytics, remote monitoring, predictive maintenance, and corporate visibility has bridged the IT and OT worlds. This convergence has created a significant challenge: IT networks are dynamic, open, and prioritized on confidentiality and integrity, while OT networks are static, deterministic, and prioritize availability and safety. Applying IT-centric security measures to OT environments is often not feasible and can even be detrimental to operations.
This interconnection has made ICS soft targets for cyberattackers. Malicious actors, ranging from state-sponsored threats to ransomware gangs, can exploit vulnerabilities in IT systems to gain a foothold and then move laterally into the OT environment.
Network Segmentation: The First Line of Defense
Network segmentation is the foundational practice of dividing a network into smaller, distinct subnetworks, or segments, each with its own security controls and access policies. In the context of ICS, this fundamentally means separating the corporate IT network from the industrial OT network.
How It Works:
-
Boundary Protection: At its core, network segmentation involves placing firewalls, gateways, and other security appliances between the IT and OT domains. This creates a hard perimeter.
-
Traffic Control: Firewalls are configured with strict access control lists (ACLs) to allow only specific, pre-approved communication between the two networks. For example, a corporate server might be allowed to collect performance data from an ICS historian database, but it would be barred from sending commands directly to a PLC (Programmable Logic Controller).
-
Protocol Filtering: Advanced segmenting solutions can understand industrial protocols (like Modbus, PROFINET, or BACnet) and perform deep packet inspection to block non-compliant traffic or potential exploits.
Benefits in ICS Security:
-
Lateral Movement Inhibition: By far the biggest advantage. If an attacker compromises a user’s workstation in the IT department, they are “trapped” within that segment. Without segmentation, they could easily scan the entire network, find OT assets, and launch attacks.
-
Reduction of Attack Surface: By isolating OT systems, you reduce the number of paths an attacker can take to reach critical infrastructure.
-
Containment of Incidents: If a malware infection or a ransomware attack does occur within the OT network, segmentation can help contain the spread, preventing it from affecting the entire industrial operation.
-
Regulatory Compliance: Many industry standards and regulations, such as NERC CIP for the power industry and IEC 62443, mandate network segmentation as a primary requirement.
Microsegmentation: Zero Trust for the OT Layer
While network segmentation is a critical first step, it can be coarse-grained. A compromised device within an OT segment might still be able to attack other devices in the same segment. This is where microsegmentation takes security to a much more granular level.
The Concept: The “Segment of One”
Microsegmentation is a security technique that creates extremely small, specific secure zones within a network, often down to the individual workload, machine, or even application level. It is a key enabler of the Zero Trust security model: “never trust, always verify.”
How It Works:
-
Identity-Based Policies: Instead of relying on network addresses (IPs) and ports, microsegmentation policies are often based on identity (e.g., this specific PLC can only talk to this specific HMI) and application context.
-
Host-Based or Fabric-Based: It can be implemented via software agents installed on endpoints (which is challenging on legacy ICS devices) or through the network fabric using virtual firewalls or software-defined networking (SDN).
-
East-West Traffic Control: While traditional segmentation focuses on North-South traffic (between IT and OT), microsegmentation controls East-West traffic – communication between devices within the OT environment.
Benefits in ICS Security:
-
Preventing OT-to-OT Attacks: It stops a compromised historian from attacking PLCs, or an HMI from attacking the SCADA server, even if they are all on the same logical network segment.
-
Securing Legacy Devices: Many legacy ICS devices cannot support modern security features like encryption or authentication. Microsegmentation can wrap a “virtual shield” around these vulnerable systems, controlling exactly who and what can interact with them.
-
Adaptive Security: Policies can be dynamic, adjusting in real-time based on the device’s behavior or a change in its security posture.
-
Simplified Management and Visibility: Modern microsegmentation platforms provide a high level of visibility into network flows, making it easier to manage and audit security policies across complex industrial environments.
The Power of Both: A Layered Defense Strategy
Network segmentation and microsegmentation are not competing technologies; they are complementary. An effective ICS security architecture uses a layered approach:
-
Broad Segmentation: Implement robust segmentation between the IT and OT networks to prevent initial entry and widespread lateral movement.
-
Microsegmentation Within OT: Within the industrial network, deploy microsegmentation to secure critical assets, isolate vulnerable legacy devices, and implement granular, least-privilege access policies.
By combining these two strategies, organizations can build a resilient, “defense-in-depth” security posture that significantly reduces the risk of a successful cyberattack on critical industrial processes, ensuring operational safety, reliability, and availability.
