The Quiet Threat: How Ransomware is Paralyzing Modern Manufacturing
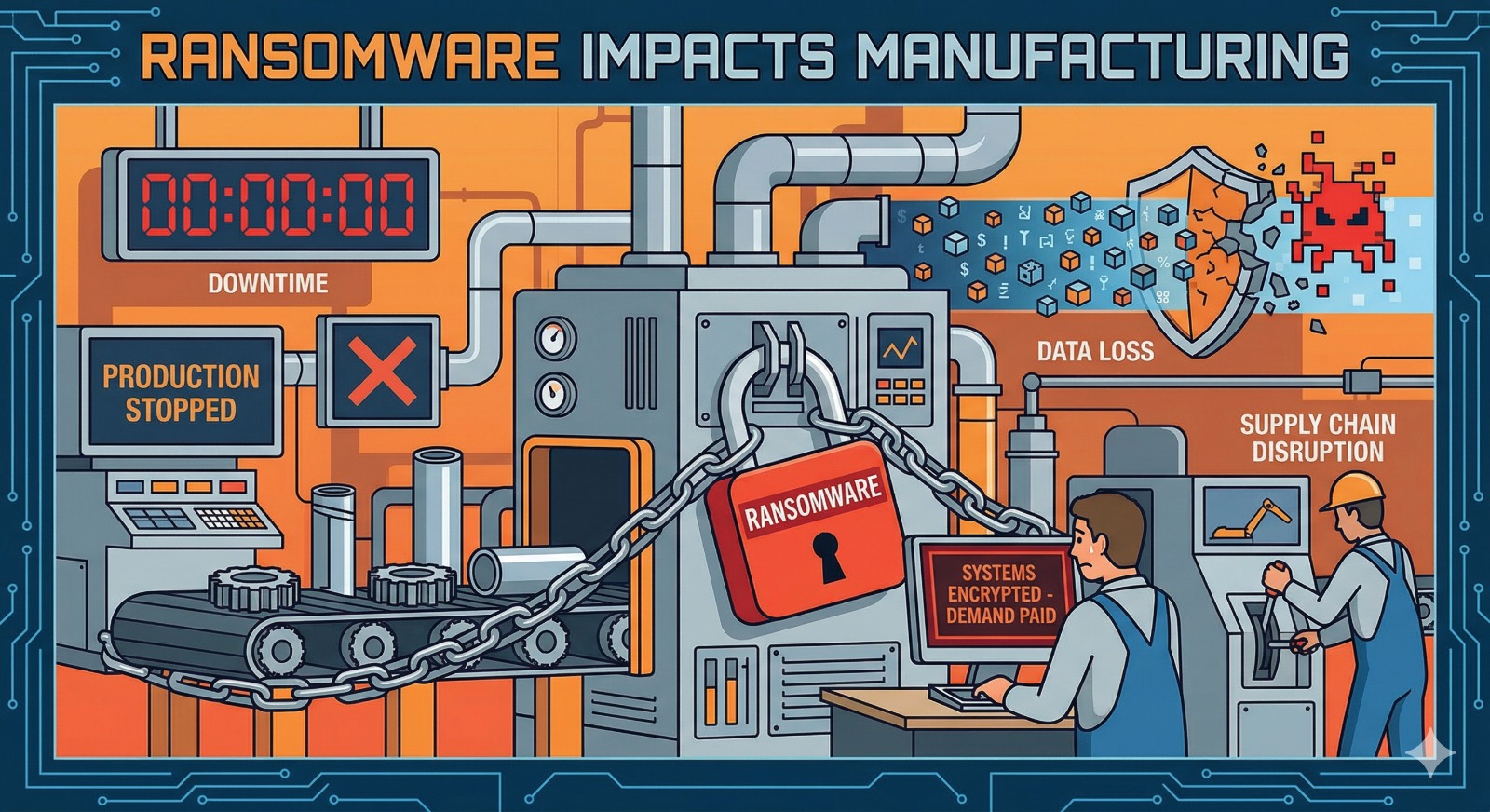
In the modern industrial landscape, the “clank and grind” of the factory floor is now inextricably linked to the “bits and bytes” of the server room. While this digital transformation has unlocked unprecedented efficiency, it has also opened a dangerous door for cybercriminals. Ransomware, once a nuisance for individual PC users, has evolved into a sophisticated weapon capable of bringing global supply chains to a grinding halt.
For manufacturing and process industries, the impact of a ransomware attack extends far beyond a simple IT headache. It is an existential threat to production, safety, and the bottom line.
1. The Death of Productivity: Unplanned Downtime
In manufacturing, time is literally money. Most modern plants operate on “Just-in-Time” (JIT) schedules. When ransomware encrypts the servers controlling the Manufacturing Execution Systems (MES) or the Enterprise Resource Planning (ERP) software, the assembly line stops.
Unlike a mechanical failure, which can be fixed with a spare part, a ransomware-induced shutdown can last for weeks. Even after a ransom is paid or systems are restored from backups, the process of “re-syncing” digital records with physical inventory can be a logistical nightmare.
2. The Convergence Risk: IT vs. OT
Historically, Information Technology (IT) (emails, spreadsheets) and Operational Technology (OT) (the sensors and controllers on machines) were kept separate. Today, they are connected to allow for real-time data analysis.
Ransomware often enters through a simple phishing email in the IT department but quickly “pivots” into the OT environment. When the Industrial Control Systems (ICS) are hit, operators lose visibility. They cannot see temperatures, pressures, or flow rates. In process industries like chemical or oil refining, this lack of visibility isn’t just a business problem—it’s a safety hazard that could lead to fires, spills, or explosions.
3. The “Double Extortion” Tactic
Hackers have moved beyond simply locking files. They now practice Double Extortion:
-
Encryption: They lock your systems so you can’t work.
-
Exfiltration: They steal sensitive blueprints, proprietary formulas, and customer contracts.
If a manufacturer refuses to pay the ransom to unlock their files, the hackers threaten to leak their Intellectual Property (IP) to competitors or the dark web. For a company whose value lies in a “secret recipe” or a patented design, this loss of IP can be more damaging than the downtime itself.
4. The Supply Chain Domino Effect
No manufacturer is an island. A hit on a single Tier-2 parts supplier can cause a “stop-ship” order for a major automotive giant thousands of miles away. We are seeing a rise in Supply Chain Attacks, where hackers target a smaller, less-secure vendor to gain a backdoor into a larger, more lucrative target. This creates a ripple effect that destabilizes entire global markets.
How Industries Are Fighting Back
The “it won’t happen to us” mentality is fading. Forward-thinking manufacturers are now focusing on:
-
Network Segmentation: Placing “firebreaks” between the office Wi-Fi and the factory floor so an infection can’t spread.
-
Immutable Backups: Keeping copies of data in a format that cannot be deleted or changed, even by someone with administrative access.
-
Incident Response Drills: Treating a cyberattack like a fire drill—practicing exactly what to do when the screens go dark.
Final Thoughts
Ransomware has turned the manufacturing sector into a primary target because the pressure to stay online makes these companies more likely to pay. However, as the industry matures, the focus is shifting from “preventing” the inevitable to “resilience”—ensuring that when a hit occurs, the factory can bounce back before the last gear stops turning.
